Redefining Trusted Remediation
for AppSec Teams
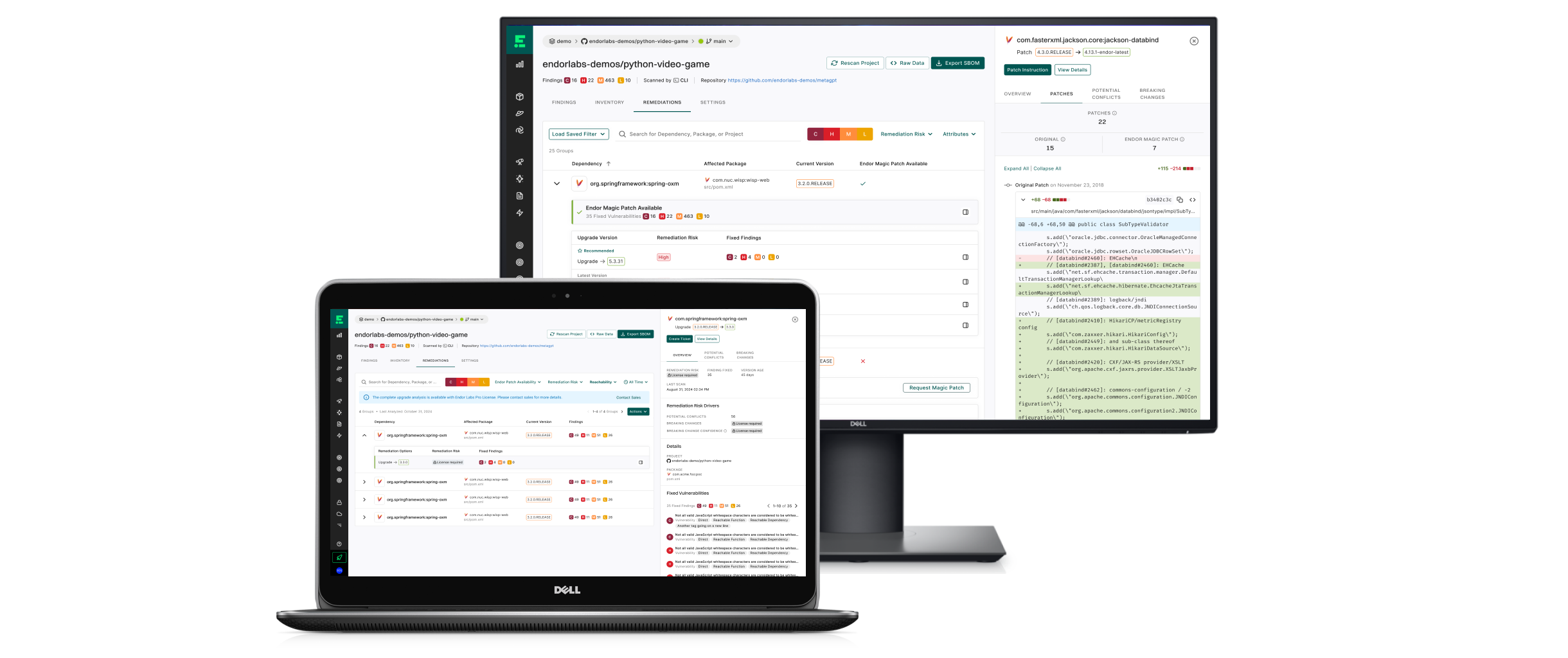
Automated Patches and Upgrade Impact Analysis
TL;DR
Led the 0→1 productization of Endor Patches and Upgrade Impact Analysis, extending Endor from vulnerability detection into trusted remediation. Built on Endor’s dependency graph, we introduced explainable automation that reduced critical CVE remediation time by 60% and rollback incidents by 80%, transforming remediation from a manual, risk-prone process into a transparent, confidence-driven workflow.
The Problem
Endor Labs helped teams detect vulnerabilities quickly. Fixing them was the bottleneck. Upgrading open-source dependencies was slow and opaque. Developers could not easily verify whether a fix truly resolved a CVE, nor could they see downstream impact before applying an upgrade. Security needed speed to meet SLAs; developers needed clarity to avoid breaking builds. The challenge became designing a remediation experience that delivered both speed and control.
From Hackathon Prototype to Platform Capability
The concept began during an internal hackathon exploring whether our dependency graph could generate safe patches automatically. The prototype demonstrated technical feasibility and strong internal interest:
Could we automatically generate safe patches using our dependency graph without breaking builds?
My role was to evolve that proof-of-concept into a scalable platform capability. This required defining a remediation interaction model, designing transparency mechanisms that would build developer confidence, and aligning engineering and product on extending Endor’s architecture beyond passive detection toward active remediation.
Extending the Architecture
Remediation required expanding the platform in two directions. We introduced a patch generation system capable of producing surgical, version-safe fixes using graph intelligence, and an impact simulation engine that modeled dependency relationships before changes were applied.
Together, these formed a unified remediation layer built on top of Endor’s detection foundation. Every action remained traceable from backend analysis through UI interaction, reinforcing consistency and confidence.
Designing for Trust
Research revealed that remediation workflows were fragmented and opaque. Developers bounced between scanners, repositories, and CI logs, often unsure whether a fix was complete or safe. We reframed remediation around a simple loop:
Actions were embedded directly into findings, pull requests, and CI notifications. Before applying any change, users could inspect diffs, review impact previews, and assess confidence signals. Automation followed understanding, not the other way around. Clarity became the mechanism for adoption.
MVP
Connecting Detection to Confident Action
The initial release focused on unifying detection and remediation within a single workflow. Rather than fully automating upgrades, we prioritized visibility and control. Developers previewed changes, examined simulations, and applied verified patches within one interface, while security teams tracked SLA progress in the same environment. This phased approach reduced friction and validated trust before expanding automation capabilities.
Outcome & Adoption
The MVP delivered measurable operational impact:
60% faster remediation for critical CVEs
80% fewer rollback incidents during dependency upgrades
Strong qualitative feedback: “predictable, transparent, safe to fix.”
Adoption accelerated once remediation actions were embedded directly into pull requests, CI notifications, and email alerts, meeting developers in their existing workflow. This initiative marked Endor Labs’ transition from vulnerability reporting to actionable remediation. It expanded the platform’s role within the software development lifecycle and strengthened its competitive differentiation.
Next Step
The foundation enables Endor’s evolution toward a fully managed remediation platform, including bulk patching across repositories, predictive upgrade safety scoring, and AI-assisted pull request generation with automated verification.